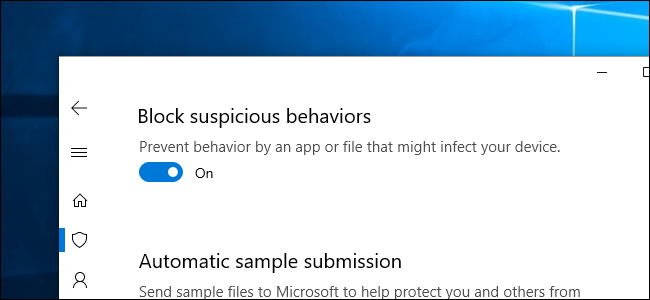
The Redstone 5 update of Windows 10 contains a new security feature named ‘Block Suspicious Behaviors’. This security aspect is intended to protect your device from suspicious behavior of any application and variety of threats. This blog will let you know how to turn on or turn off the Block Suspicious Behaviors feature preventing any file or app to infect your device. […]
security
How to Prevent Online Security Threats

Most users are unaware of the cyber-attacks lurking on the web, partly because online security prevention cannot be shown practically. Maintaining the cyber security should be our utmost priority.
Cyber criminals not only target businesses but also focuses on government officials, popular people, small organizations, and users. […]
KRACK Wi-Fi Security Attack: WPA2 Wi-Fi Network Vulnerability

Most wireless connections are secured with the Wi-Fi Protocol Acess. WPA2 (Wi-Fi Protocol Access 2) encrypts the connection between a PC or Smartphone and Wi-Fi Access Point to make your browsing safe. But this encrypted connection can be cracked, it is feasible for somebody to read what is transmitted over the network, permitting them to intercept the passwords or credit card details or to infuse malicious code when user visit websites. […]
How to Use a Bluetooth in a Secure Way

Bluetooth is a short-range wireless technology which integrates with other Bluetooth enabled devices within the range of 10 meters including smartphones, notebook, headphones, computers, and PDAs. In today’s era, Bluetooth has become the most common technology among the worldwide users. […]